Defender for Cloud offers comprehensive security management and threat protection for your hybrid and multi-cloud workloads. The free features focus on securing your Azure resources specifically, while additional paid plans provide enhanced protection for your on-premises infrastructure and resources across different cloud platforms. With Defender for Cloud, you can achieve unified security and peace of mind across your entire IT environment, regardless of its composition and location.
Follow this link to enable Defender for Cloud for Azure workloads: https://learn.microsoft.com/en-us/azure/defender-for-cloud/get-started.
Since Microsoft offers Defender for Cloud through the Microsoft Azure portal, it becomes super-easy to enable it for Azure workloads, and for other cloud environments, the process remains like other CSPM tool processes.
Prerequisites
- You need an active subscription to Microsoft Azure to utilize Microsoft Defender for Cloud.
- Ensure you have appropriate permissions and access to manage Azure resources. You should have an Owner, Contributor, or Reader role assigned for the subscription or for the resource group that the resource is located in.
Enable Defender for Cloud on your Azure subscription
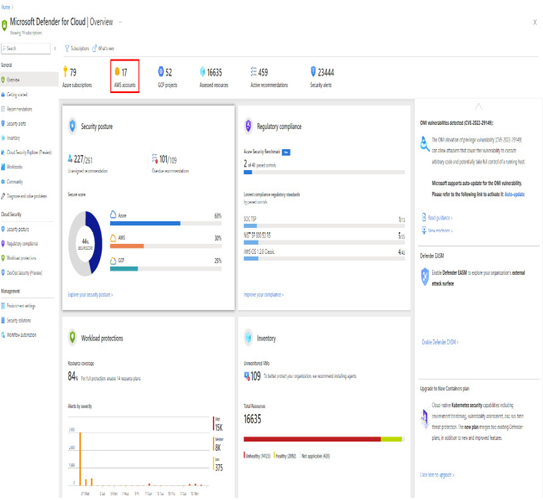
Once you follow the steps mentioned in the preceding link, Defender for Cloud gets enabled on your subscription and you have access to the basic features provided by Defender for Cloud, such as the Foundational CSPM plan, recommendations, access to the asset inventory, workbooks, Secure Score, and regulatory compliance with the Microsoft cloud security benchmark. The other important links are provided at the end of the chapter under the Further reading section.
Let us now understand how to onboard GCP accounts to Microsoft Defender for Cloud.
Onboarding GCP accounts
Microsoft Defender for Cloud provides robust protection for workloads hosted on Google Cloud Platform (GCP). However, it is necessary to establish a connection between your Azure subscription and GCP to leverage these security services effectively.
Follow this link to enable Defender for Cloud for GCP projects: https://learn.microsoft.com/en-us/azure/defender-for-cloud/quickstart-onboard-gcp#connect-your-gcp-project.
Prerequisites
- You need a Microsoft Azure subscription as Microsoft offers the Defender for Cloud service through the Azure portal.
- Microsoft Defender for Cloud on your Azure subscription must be enabled.
- You need access to a GCP project.
- You need to have a Contributor role on the relevant Azure subscription and an Owner role on the GCP organization or project.
- It is possible to connect your GCP projects to Microsoft Defender for Cloud on the project level and also connect multiple projects to one Azure subscription. You can connect multiple projects to multiple Azure subscriptions as well.
Steps to onboard GCP accounts
Once you follow the steps mentioned in the preceding link, you will be able to establish a connection between your GCP project and Defender for Cloud and then a scan starts on your GCP environment. New recommendations will appear in Defender for Cloud after up to six hours. When auto-provisioning is enabled, Azure Arc and any enabled extensions are automatically installed for each newly detected resource.
Let us now look at some important points related to other environments.